Biometric QR phone flow
Best when the deployment wants the customer to complete age and identity verification on a phone before the machine releases the gated checkout path.
VendingTracker supports age-restricted deployments where the machine must sit inside a controlled workflow for verification, logging, and operator oversight.
The deployment path starts with machine model, workflow requirements, verification approach, and the regulatory environment rather than with vague claims about age gating.
Age-restricted vending has to do more than dispense product. The machine, verification method, logging posture, and payment flow all have to work together without creating a clumsy customer experience or a weak compliance story.
That is why the strongest buyers start with the real verification workflow first, then assess machine fit, rollout environment, and operator controls.
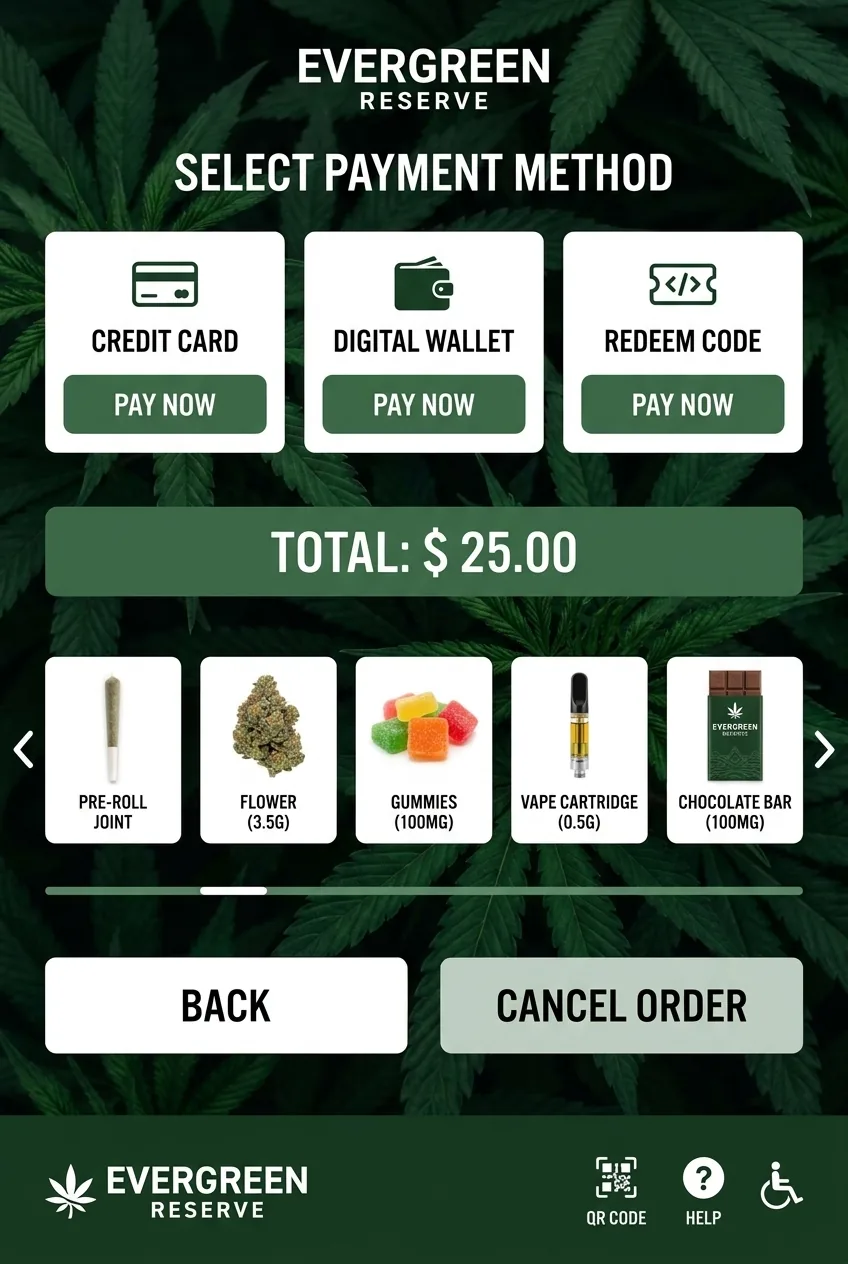
DMVI already has a live biometric age-verification flow where the machine displays a QR code, the shopper scans it on their phone, completes age and identity verification on the device, and then returns to the machine to finish the transaction.
That matters because buyers can review the full sequence as an actual consumer journey rather than a theoretical integration diagram.
One deployed path uses biometric phone-based verification after a machine-side QR prompt. That is useful when the deployment wants stronger identity assurance without forcing the machine itself to handle every verification step locally.
A simpler path also exists where the consumer swipes a US driver license at the machine, the software calculates age, ungates the product, and allows checkout directly on the screen. The right answer depends on jurisdiction, product category, fraud posture, and the customer experience you are trying to create.
Best when the deployment wants the customer to complete age and identity verification on a phone before the machine releases the gated checkout path.
Best when the deployment prefers a faster on-machine experience where a US driver license swipe confirms age and unlocks the purchase flow locally.
Age verification is not just a scanner question. The platform also has to manage product gating, event logging, payment enablement after approval, and the administrative logic around how the machine behaves when verification fails or times out.
VendingTracker is useful here because it can sit across the verification trigger, the machine-side UX, and the operating controls that determine what the team can review later.
Verification method, deployment geography, machine hardware, payment path, and reporting requirements all need to be scoped together. That is especially true when the machine must support a more sensitive retail or public-access use case.
A good review should also answer what happens when verification fails, how fallback is handled, and which evidence the operator needs available after the event.
Age-restricted vending software is the management and control layer used to support regulated products with verification workflows, logging, and deployment controls.
Yes. Vape and tobacco deployments can be assessed where age-verification integration, monitoring, and access-control workflows are required.
VendingTracker can support more than one age-verification path, including a biometric QR flow where the shopper verifies on a phone and a simpler swipe-ID flow where a US driver license confirms age and ungates checkout on the machine.
Vape, tobacco, alcohol, cannabis in permitted environments, and other regulated product categories often require age-restricted workflow support.
VendingTracker supports workflow logging and reporting as part of the operator control layer, with the exact data points defined during deployment scoping.
Book a demo, request a compatibility review, or start an integration conversation with the right technical context from the start.